Automated
Machine Trust
Prevent attacks caused by compromised API credentials.
Protect all of your applications, services and data with a zero trust architecture.
Zero Trust API Security
Over 80% of web traffic is API traffic. Secure access between API services and their clients.
Dynamic Identity
Automated,
Humanless MFA
Centralized Control
What Industry Leaders Say About Us
Corsha aims to mitigate [API secret] difficulties by adding an extra layer of security on top of API secret-focused solutions, brokering machine access, and depriving hackers of the opportunity to target APIs through zero-trust authentication.

Tim Keary
VentureBeat
An Identity-First Security Layer
Corsha isn’t an alternative to secrets management, but instead a security layer on top of your current methods in order to greatly reduce the API attack surface. Corsha’s platform abstracts the security vulnerabilities that often stem from poor API secrets hygiene.
An Environment Agnostic Solution
Whether you are running a legacy, monolithic application or run in microservices environments, Corsha has you covered. Running on a public cloud, on premise or hybrid? No problem. Corsha is built for all of the places you run your workloads.
Clear Visibility
& Control
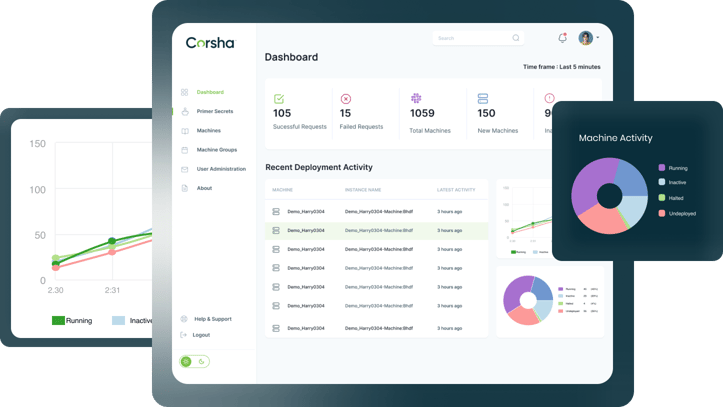
Corsha’s central admin console provides full visibility and control into all of the machines that are accessing your APIs and when their identities were last rotated. Halt or pause access for a machine or group of machines
at the drop of a hat.




