The only Machine Identity Provider Purpose-Built for
Corsha securely connects the operational systems that run our world, so OT enterprises can stop attacks in real time, automate identity security, and modernize with confidence.
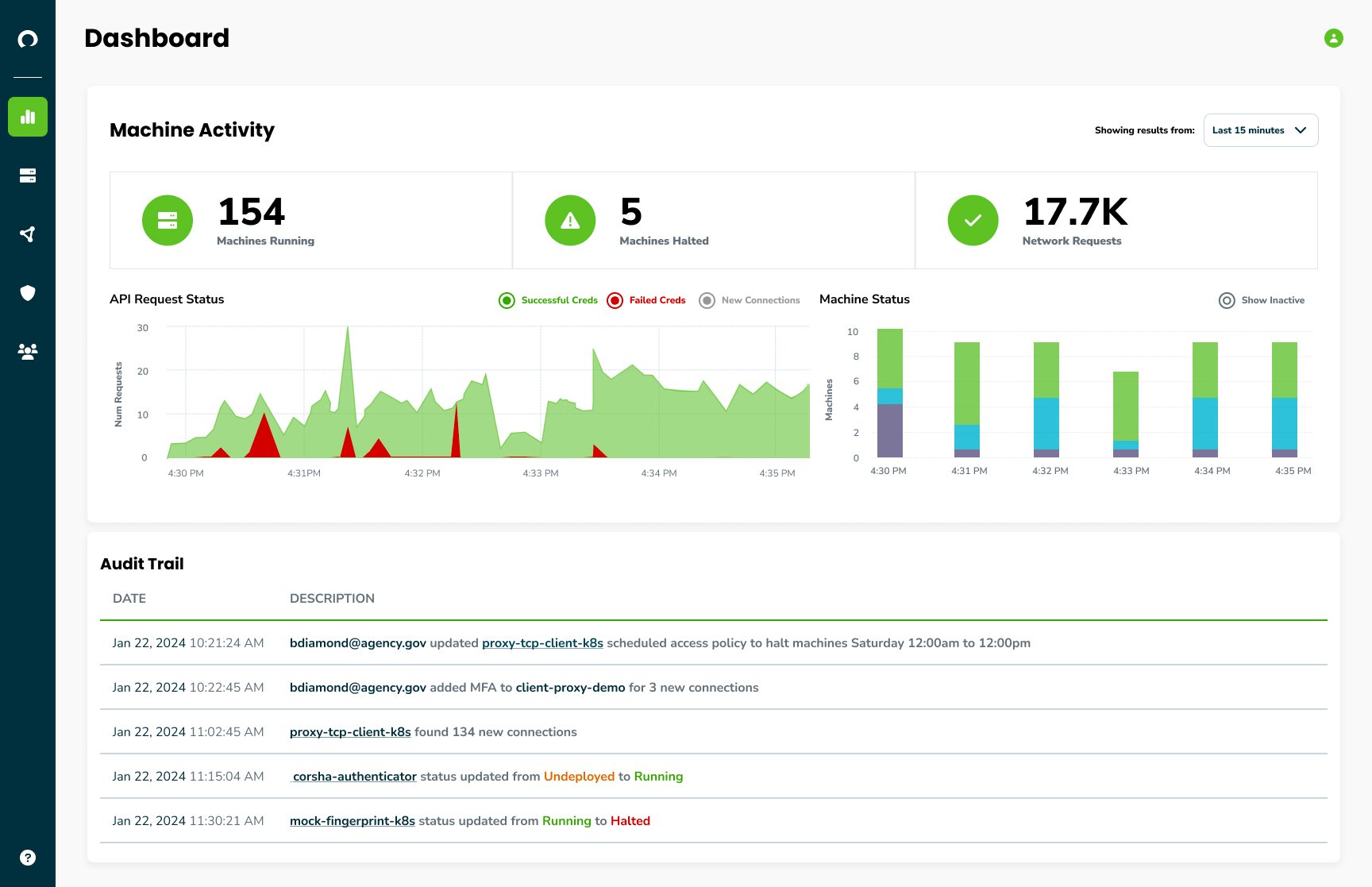
Level up from OT visibility to identity-driven action with Corsha mIDP
-1.png?width=267&height=191&name=Vector%207%20(1)-1.png)
Dynamic Machine Identities
Give every machine a verifiable identity so OT teams can continuously verify machine-to-machine communication across legacy and modern operational systems, without relying on static network assumptions or manual access controls.
.png?width=267&height=191&name=Vector%209%20(1).png)
Connection Discovery
Automatically discover every machine and every connection across operational environments. Corsha eliminates blind spots, captures connection activity, and provides audit-ready evidence for security, operations, and compliance teams.
-1.png?width=267&height=191&name=Vector%207%20(1)-1.png)
Dynamic Authentication
Continuously verify every automated machine connection before communication is allowed. Corsha enables identity-based microsegmentation to prevent unauthorized access and lateral movement before attackers can compromise operational systems or disrupt production.
.png?width=267&height=191&name=Vector%209%20(1).png)
Intelligent Access Control
Apply identity-based policies at the connection level so only verified and necessary machine communication is allowed. Corsha baselines behavior, analyzes context, and enables real-time action without rearchitecting OT networks or touching control logic.
-1.png?width=267&height=191&name=Vector%207%20(1)-1.png)
Deploy Anywhere
Deploy Corsha the way your operational environment requires, including SaaS, hybrid, and on-premises options. Corsha supports modern, legacy, distributed, and highly controlled environments without disrupting uptime, resilience, or modernization plans.
Ready to learn more? Dive into the future of Machine Identity Security for operational systems
WHY?
Your core communication is machine-to-machine, over 90% in fact.
That is why every machine connection across your industrial network, applications, enterprise, and cloud needs to be verified in real time.

0%
Trusted By










Real reviews, real results—find out why customers rely on Corsha.
%20(1)%20(1).jpg?width=1200&height=1284&name=imgpsh_fullsize_anim2%20(1)%20(1)%20(1).jpg)
William Potter
Lead Engineer, Federal
Since implementing Corsha solutions in our zero trust lab demo environment for Lumen’s public sector customers, our zero trust lab architecture has been significantly enhanced. Corsha’s platform for non-human identity has enabled us to secure long-lived API secrets and obtain visibility on client connections.
Awards





Resources
Explore the latest in Machine Identity Security resources. Discover articles, white papers, case studies, and more to level up.
