The ongoing digital transformation, often referred to as Industry 4.0, is fundamentally changing traditional industrial systems. This wave of innovation affects various aspects, including manufacturing and supply chain management, making the integration of digital technologies not just an option but a necessity to remain competitive in today's fast-paced world.
Several key factors are driving the adoption of digital technologies in industrial systems:
- Operational Efficiency: Applying modern data analytics, system modeling, AI/ML techniques, and more can enable streamlined operations, reduce downtime, minimize errors, and enhance overall efficiency.
- Data-Driven Insights: The ability to collect and analyze vast amounts of data empowers decision-makers with actionable insights for informed choices.
- Predictive Maintenance: Connecting devices together and monitoring the data they produce in real-time helps prevent equipment failures or downtime.
- Supply Chain Optimization: Digital systems enhance transparency, enabling companies to optimize supply chains, reduce costs, and respond to market demands swiftly.
- Enhanced Safety: Automation and AI-powered systems improve workplace safety by handling hazardous tasks and identifying potential risks.
The Challenges
As organizations increasingly embrace digital transformation within their industrial workflows, a new challenge arises: securing the communication between Operational Technology (OT) and Information Technology (IT) systems. Let's delve into the challenges one by one:
- Legacy Infrastructure Compatibility: Legacy OT systems often predate modern IT frameworks, resulting in compatibility issues. These systems were designed with functionality in mind rather than cybersecurity, making them vulnerable to modern threats. Integrating these systems with IT networks requires bridging the gap between outdated protocols and modern security standards.
- Varying Security Postures: OT and IT systems have traditionally been governed by different security postures. While IT systems are accustomed to frequent updates and patches, OT systems often remain static for stability reasons. This divergence leads to different security vulnerabilities and approaches. Aligning these disparate security practices and methodologies poses a significant challenge when aiming for a cohesive security strategy.
- Real-Time Constraints: OT systems operate in real-time environments where microseconds can make a difference. Security measures that introduce latency or disrupt processes can lead to catastrophic consequences. Securing OT to IT communication without impacting the timely flow of critical data demands a careful balance between security and operational efficiency.
- Lack of Standardization: In the realm of OT, a lack of standardized protocols and frameworks hinders the implementation of uniform security measures. Unlike IT, where standardized practices are more prevalent, OT systems vary widely across industries and organizations. This diversity makes it challenging to implement consistent security measures that cater to the unique needs of each system.
- Asset Complexity: Industrial environments encompass a diverse array of assets, from legacy machinery to modern IoT devices. Each asset may have different security capabilities and requirements. Managing the security of these diverse assets while ensuring a holistic approach to OT to IT communication is a formidable challenge. Furthermore, as industries adopt Industry 4.0 technologies, the number and complexity of assets continue to grow, compounding the challenge.
Securing OT to IT Communication
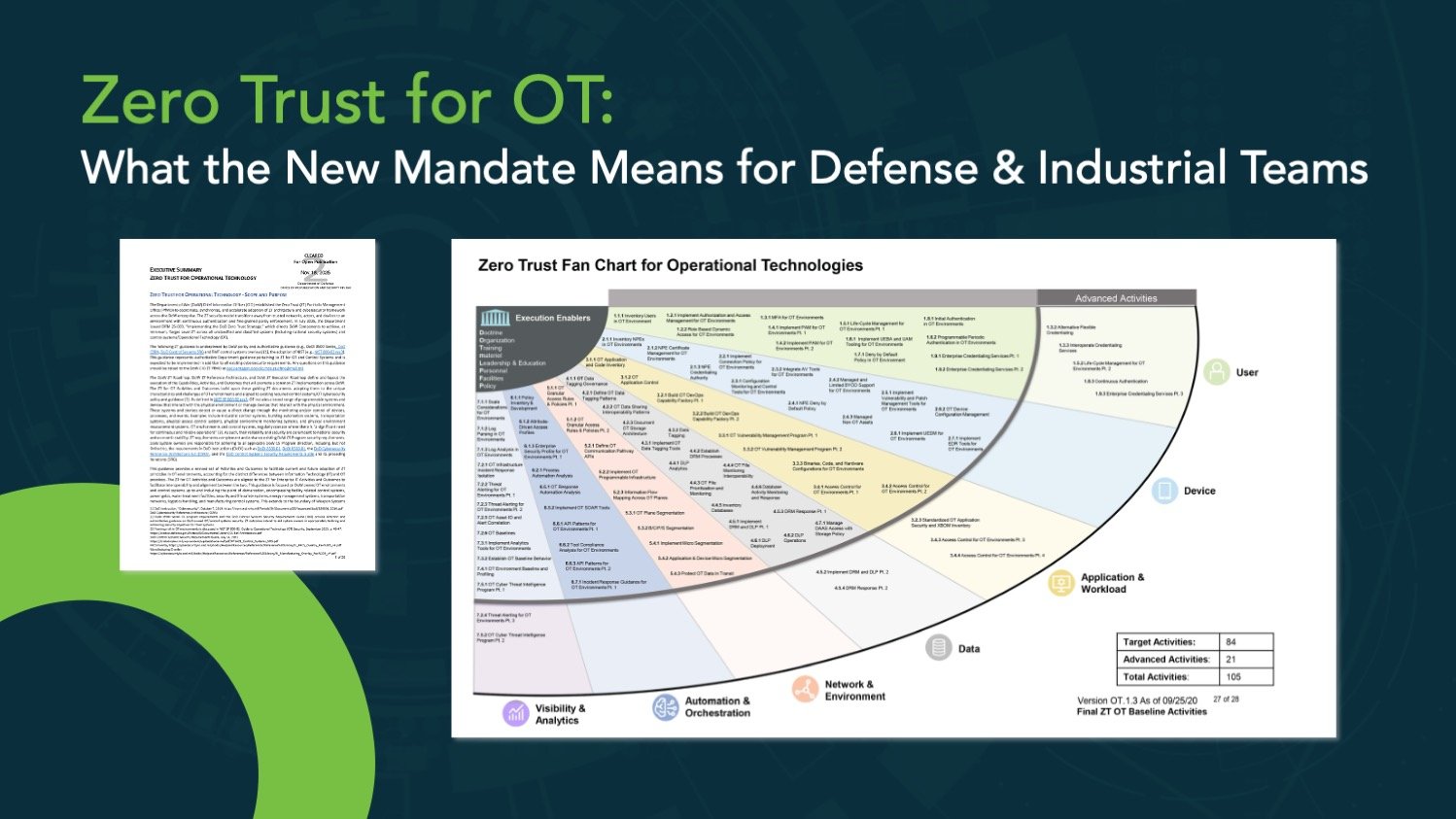
From implementing a Zero Trust approach to encryption and multi-factor authentication, there are a range of strategies organizations can adopt to enhance the security of OT to IT communication.
Securing OT to IT communication is a complex task with challenges arising from legacy systems, differing security approaches, real-time demands, lack of standardization, and complex assets. Addressing these issues requires a strategic approach that balances security, operational efficiency, and industry-specific requirements.
Learn strategies for securing OT to IT communications in our new whitepaper, From Legacy to Leading Edge: Challenges and Solutions for OT to IT Security
Corsha’s Approach to Securing OT to IT Communication
Corsha's Zero Trust Platform offers a cutting-edge solution for advancing API and machine-to-machine security. It introduces the industry's first dynamic and fully automated Multi-Factor Authentication (MFA) for APIs, ensuring that organizations can protect their APIs within complex and dynamic environments like the cloud and edge computing.
What sets Corsha apart is its ability to bring the proven security benefits of MFA, which have been successful with human users, into the realm of APIs and manufacturing protocols. This dynamic and continuous verification process is a fundamental element of zero-trust frameworks, enhancing the overall security posture.
Corsha provides both hardware and software-based connectors, making it a versatile and easy-to-implement solution. No modifications to manufacturing equipment are required, simplifying the adoption process. This flexibility makes Corsha a valuable security enabler for automating critical workflows and data movement across networks.
The core of Corsha's technology lies in its Distributed Ledger Network (DLN). When deployed, the lightweight Connector establishes a dynamic authentication stream within the DLN, creating a unique machine identity for each API client. This identity facilitates easy verification, monitoring, and control through Corsha's central Administrative Console.
Corsha's platform addresses essential security drivers, including protection against machine-to-machine exploits like man-in-the-middle attacks and API credential stuffing. It also acts as a catalyst for enhancing security and automation in data movement workflows across diverse networks, providing dynamic machine identities for API clients and a unified view of machines in hybrid deployments. Additionally, it offers precise control over API access on a per-machine basis, and excels in creating secure, API-only connections, even for machines that may have pre-existing, non-standard, or inadequate connectivity and security measures.