Blog
By Anusha Iyer
on December 18, 2025
on December 18, 2025
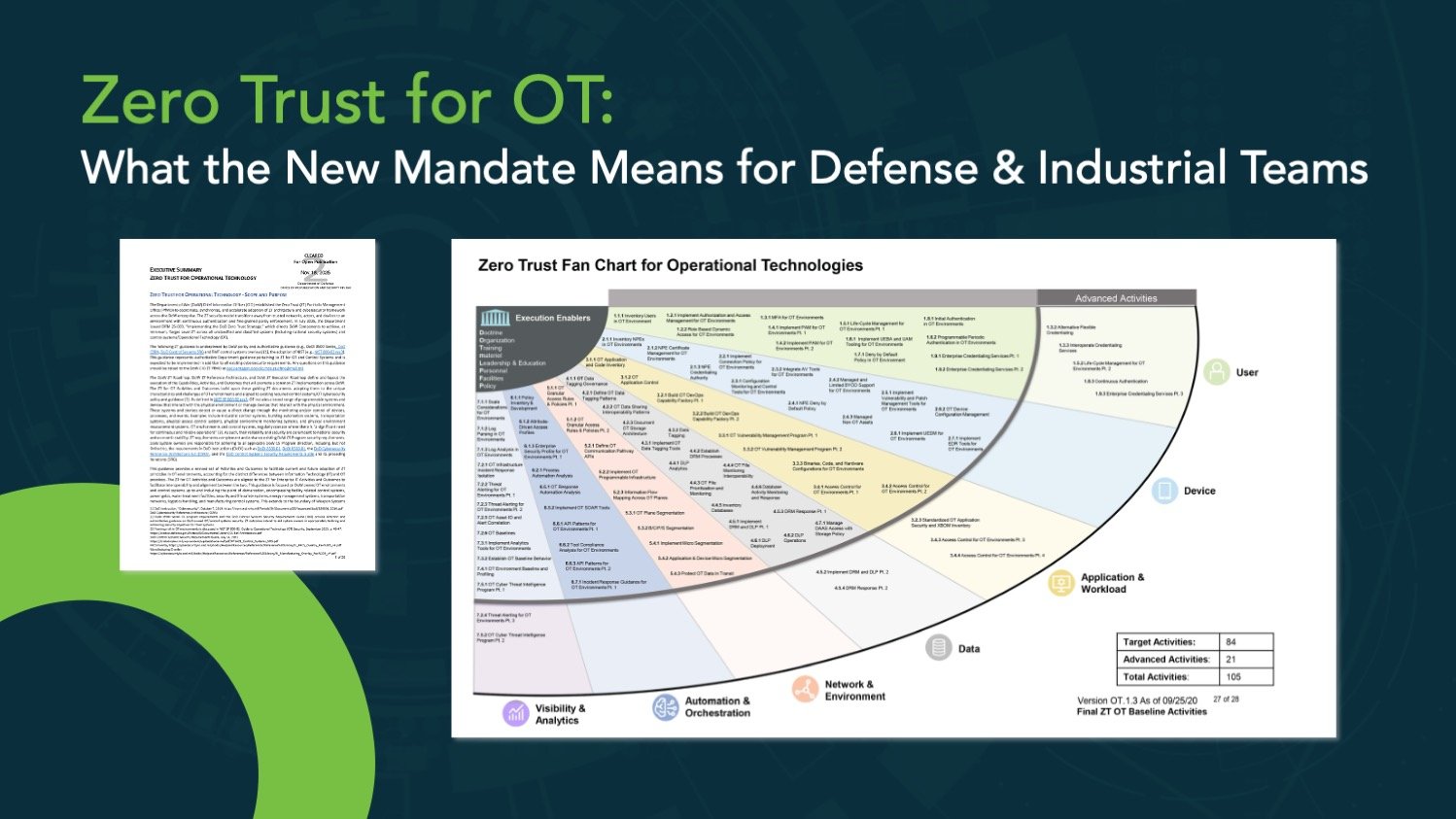
By Brian Reed
on November 03, 2025
on November 03, 2025
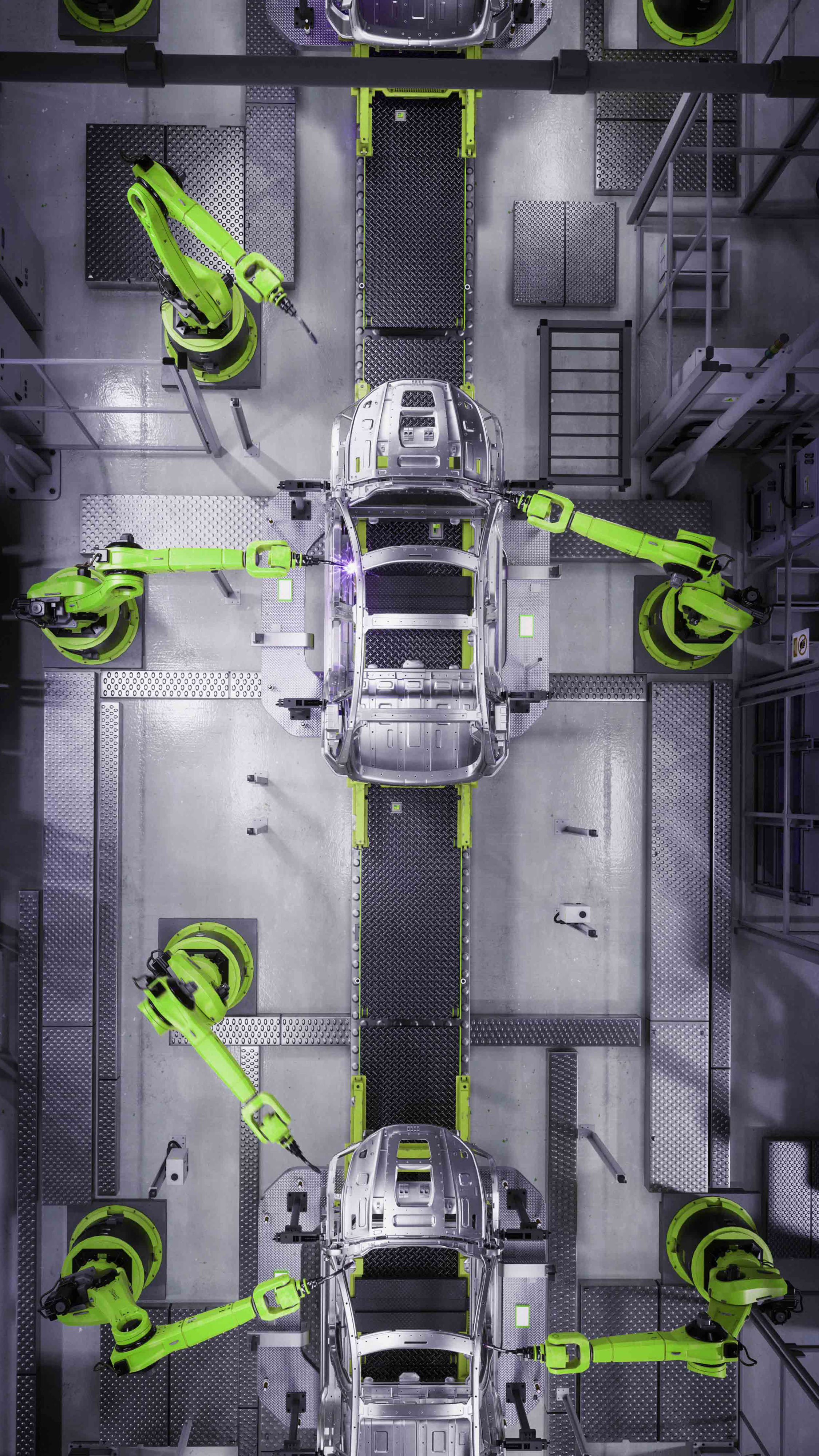
By David Mazary
on June 27, 2025
on June 27, 2025
By Chris Parlette
on June 17, 2025
on June 17, 2025
By Chris Parlette
on March 18, 2025
on March 18, 2025
By Joel Krooswyk
on February 03, 2025
on February 03, 2025
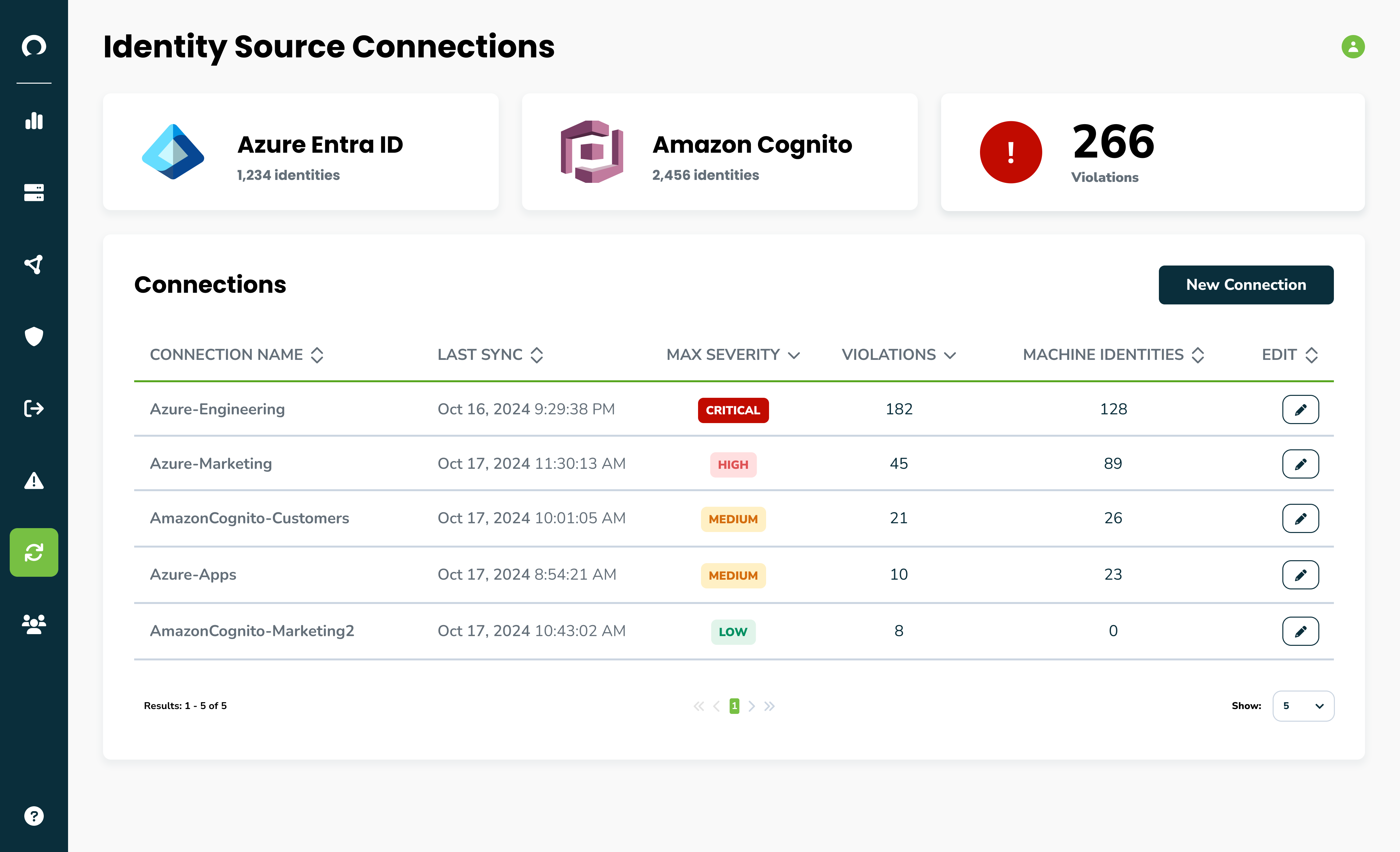
By Andrew Dubbs
on January 18, 2025
on January 18, 2025

By Corsha
on January 18, 2025
on January 18, 2025





-1.png)
